9 Critical Ways to avoid Crypto Scams in 2026 and Protect Your Assets
To avoid crypto scams in 2026, investors must understand a key reality: most losses are not caused by protocol failures, but by behavioral vulnerabilities and social engineering.
As the crypto ecosystem matures, scam techniques evolve in parallel. Attackers increasingly combine:
- phishing interfaces
- fake protocols
- impersonation strategies
- malicious smart contracts
This makes security less about tools and more about decision frameworks.
This guide provides a structured approach to avoid crypto scams in 2026, focusing on mechanisms rather than isolated cases.
Understanding How Crypto Scams Work
Crypto scams are not random—they follow repeatable patterns.
Core Attack Vectors
| Attack Type | Mechanism | Outcome |
|---|---|---|
| Phishing | Fake interfaces or links | Wallet compromise |
| Smart Contract Exploit | Malicious approvals | Token draining |
| Social Engineering | Impersonation | User manipulation |
| Fake Projects | Misleading narratives | Capital loss |
These patterns are consistently observed across the ecosystem.
Scam Lifecycle (Framework)
This lifecycle model provides a structured way to avoid crypto scams in 2026 by identifying risk at each stage.
How Attacks Typically Unfold
- Attraction
- social media, ads, influencers
- Trust Building
- fake branding, UI copies, testimonials
- Action Trigger
- connect wallet / approve transaction
- Execution
- funds drained or access compromised
- Disappearance
- project or attacker vanishes
Understanding this lifecycle is essential to avoid crypto scams in 2026.

9 Critical Ways to Avoid Crypto Scams in 2026
1. Never Trust Interfaces Without Verification
Always verify:
- URLs
- domain spelling
- official sources
Fake interfaces are often visually identical.
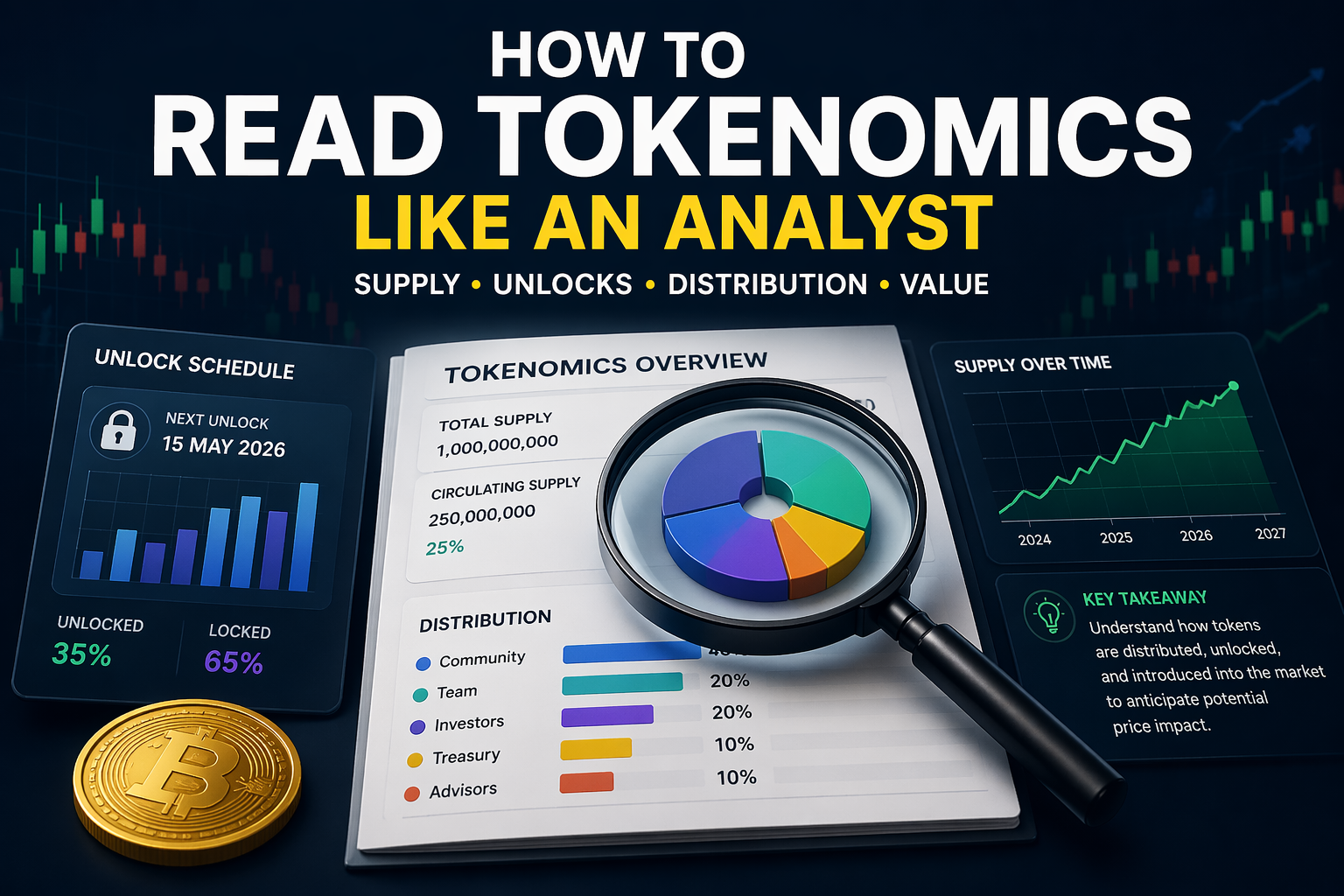
2. Understand What You Sign
Before approving any transaction:
- read permissions
- check contract interactions
Blind signing remains one of the most common mistakes.
3. Separate Storage and Interaction
Use:
- hardware wallet → storage
- hot wallet → interaction
This limits exposure.
For long-term asset protection, many investors rely on hardware wallets like Ledger to isolate private keys from online interactions and reduce exposure to phishing risks.
4. Avoid Urgency-Based Decisions
Scams rely on:
- fear of missing out
- time pressure
Any urgent action = red flag.
5. Verify Information Across Sources
Never rely on a single source.
Check:
- official websites
- community channels
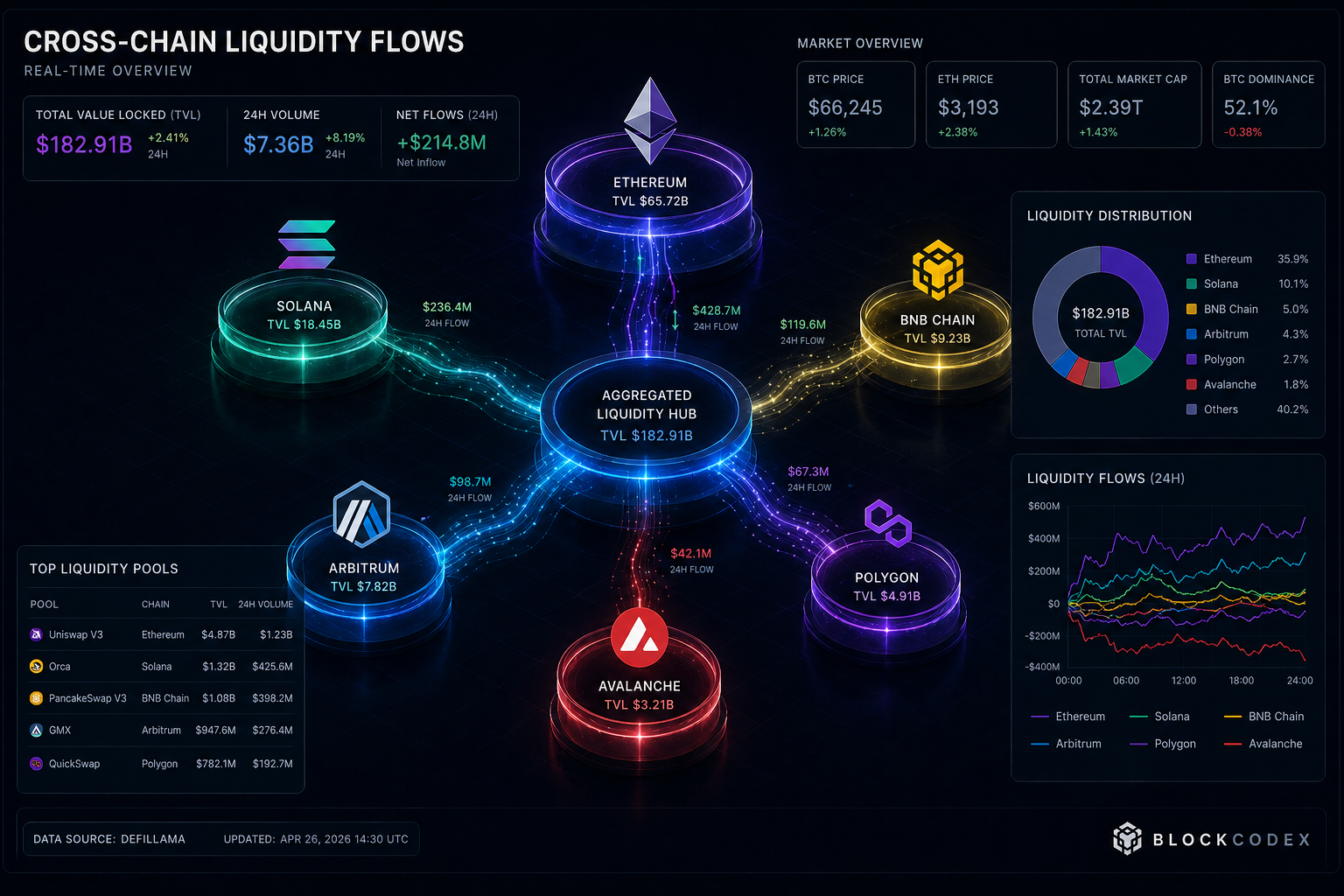
- trusted analytics platforms
6. Limit Wallet Exposure
Do not connect your main wallet to:
- unknown dApps
- experimental platforms
Use secondary wallets when needed.
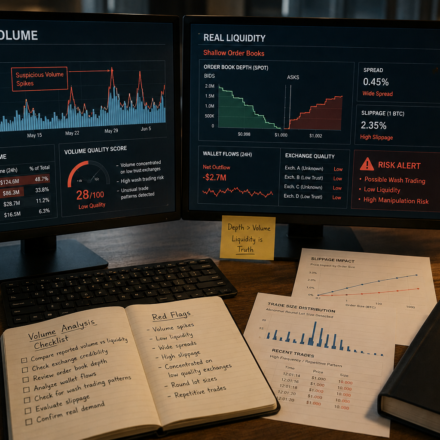
7. Monitor Token Approvals
Many attacks exploit unlimited approvals.
Regularly:
- review permissions
- revoke unnecessary access
8. Be Cautious With Social Channels
Scammers frequently use:
- Discord
- Telegram
- X (Twitter)
Impersonation is common.
9. Build a Security Routine
Security must be systematic:
- regular checks
- structured processes
- consistent habits
Practical Application: Daily Security Checklist
Minimal Routine
- verify URLs before interaction
- use separate wallets
- review approvals weekly
- avoid reacting to urgency
Advanced Routine
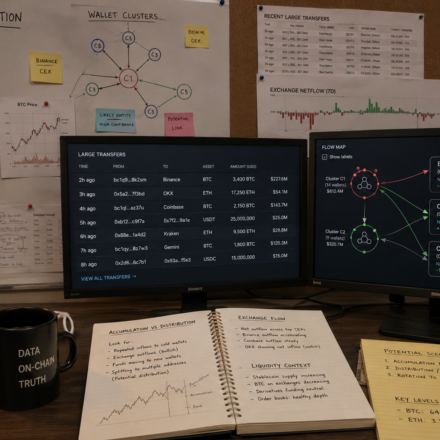
- track wallet permissions
- monitor suspicious transactions
- use analytics tools
- isolate high-value assets
Applying this checklist consistently is one of the most reliable ways to avoid crypto scams in 2026 in practice.
Tool Insight: Reducing Attack Surface
Ledger
To avoid crypto scams 2026, reducing exposure is critical.
Hardware wallets such as Ledger help by:
- isolating private keys
- enforcing transaction validation
- reducing remote attack vectors
However, they do not eliminate risk entirely. Security still depends on how users interact with protocols.
Advanced Insight: Scams Are Behavioral Systems
A key observation:
👉 Most scams do not exploit code—they exploit decision-making gaps.
This means:
- knowledge > tools
- process > reaction
- discipline > speed
Understanding this is essential to avoid crypto scams in 2026.
Common Mistakes to Avoid
- trusting visual interfaces
- ignoring transaction details
- overexposing wallets
- reacting to urgency
- relying on a single source
Conclusion
To effectively avoid crypto scams 2026, investors must shift from reactive behavior to structured decision-making.
Security is not a single action but a system combining:
- awareness
- verification
- controlled interaction
As the ecosystem evolves, those who adopt disciplined frameworks will significantly reduce their exposure to risk.
For a deeper understanding of security risks and behavioral patterns, see our guide on “7Critical Crypto Security Mistakes That Cost Investors Millions“.
FAQ
What is the most common crypto scam?
Phishing remains the most common, often through fake interfaces and impersonation.
Are hardware wallets enough to stay safe?
They improve security but do not prevent user errors or phishing.
Can scams be completely avoided?
Risk can be reduced significantly, but never entirely eliminated.